

HashiCorp Vault is a powerful secrets management platform that securely stores and issues short-lived credentials, provides encryption as a service, and maintains fine-grained access controls. Teams running Vault in Kubernetes can automatically inject secrets into applications, benefiting from dynamic secret rotation and robust audit logging. But while Vault offers strong security capabilities, upgrading it in a Kubernetes environment brings risks: configuration deprecations, plugin incompatibilities, or potential downtime if unseal and replication steps aren’t carefully orchestrated.
In this post, we’ll explore how Chkk’s Operational Safety Platform delivers a comprehensive solution for managing Vault upgrades—from curated release notes and preflight checks to structured Upgrade Templates, preverification, and more. By using Chkk, you can confidently keep Vault secure and up to date while minimizing disruptions.
Chkk continuously monitors official Vault releases, pulling out the must-know changes that affect secrets storage, authentication methods, and policy behavior. Instead of sifting through lengthy release notes, you get concise insights—like new database engines, CLI flag deprecations, or critical security patches—so you can quickly assess whether an update is urgent or introduces new features your team might want to adopt.
Before you upgrade, Chkk’s preflight checks verify that your current environment meets the upcoming version’s requirements. It looks at your storage backend configuration, TLS settings, token usage, and any secrets engines or auth methods that might be deprecated. Postflight checks run after the upgrade, ensuring Vault unseals correctly, logs no major errors, and that tokens and secrets engines still function as expected. This automated validation helps catch pitfalls—like misconfigurations that leave Vault sealed or break existing tokens.
Chkk proactively tracks Vault’s release lifecycle, warning you when your deployed version lacks security patches or is nearing end-of-life. It compares official guidance against your environment—like your Kubernetes version or integration with cloud providers—so you’re always running a stable, supported Vault release. Staying current mitigates security exposures and avoids unsupported features that might put your secrets at risk.
For robust Vault upgrades, Chkk supports both:
Each template details the exact steps, including data backups, unseal procedures, health checks, and rollback instructions.
Major or sensitive updates often warrant a “practice run.” Chkk’s preverification simulates your Vault configuration—auth backends, secrets engines, policies—in a safe environment. By applying the new version in a sandbox, Chkk identifies incompatibilities such as deprecated configuration parameters or plugin mismatches before they hit production. Early detection helps fix potential issues well before you’re managing them under pressure in a live environment.
Whether Vault is installed via Helm, Kustomize, or raw YAML, Chkk can parse your manifests and values to orchestrate safe and reliable upgrades. Chkk respects private registries, custom images, and your organization’s security constraints, ensuring you don’t have to refactor your preferred deployment approach just to keep Vault up to date.
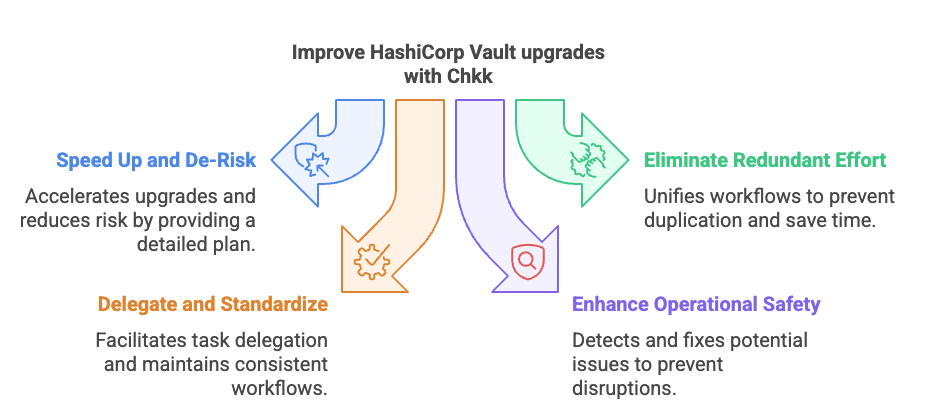
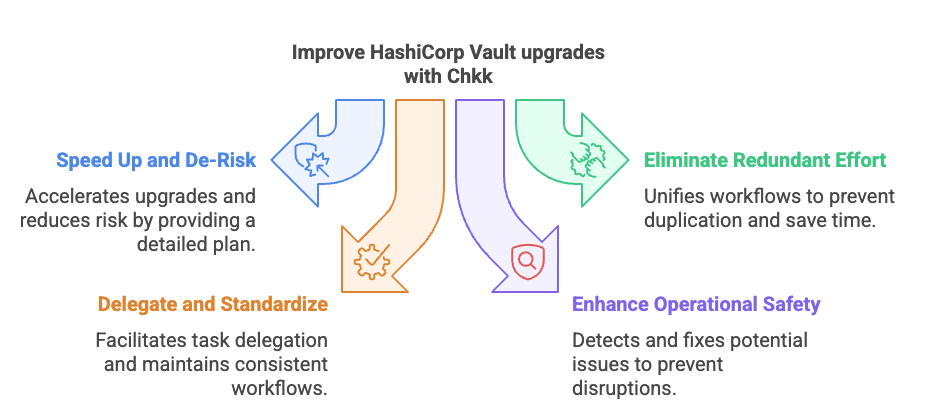
Chkk Operational Safety Platform simplifies upgrades, reduces risk, and keeps your Kubernetes infrastructure operational. Here’s how that applies to HashiCorp Vault upgrades:
Try Chkk Upgrade Copilot to experience how these extended capabilities can simplify your upgrade processes for HashiCorp Vault and 100s of other Kubernetes add-ons. We look forward to helping you achieve seamless, secure, and efficient operations.
Click the button below to book a demo and learn more.
HashiCorp Vault is a powerful secrets management platform that securely stores and issues short-lived credentials, provides encryption as a service, and maintains fine-grained access controls. Teams running Vault in Kubernetes can automatically inject secrets into applications, benefiting from dynamic secret rotation and robust audit logging. But while Vault offers strong security capabilities, upgrading it in a Kubernetes environment brings risks: configuration deprecations, plugin incompatibilities, or potential downtime if unseal and replication steps aren’t carefully orchestrated.
In this post, we’ll explore how Chkk’s Operational Safety Platform delivers a comprehensive solution for managing Vault upgrades—from curated release notes and preflight checks to structured Upgrade Templates, preverification, and more. By using Chkk, you can confidently keep Vault secure and up to date while minimizing disruptions.
Chkk continuously monitors official Vault releases, pulling out the must-know changes that affect secrets storage, authentication methods, and policy behavior. Instead of sifting through lengthy release notes, you get concise insights—like new database engines, CLI flag deprecations, or critical security patches—so you can quickly assess whether an update is urgent or introduces new features your team might want to adopt.
Before you upgrade, Chkk’s preflight checks verify that your current environment meets the upcoming version’s requirements. It looks at your storage backend configuration, TLS settings, token usage, and any secrets engines or auth methods that might be deprecated. Postflight checks run after the upgrade, ensuring Vault unseals correctly, logs no major errors, and that tokens and secrets engines still function as expected. This automated validation helps catch pitfalls—like misconfigurations that leave Vault sealed or break existing tokens.
Chkk proactively tracks Vault’s release lifecycle, warning you when your deployed version lacks security patches or is nearing end-of-life. It compares official guidance against your environment—like your Kubernetes version or integration with cloud providers—so you’re always running a stable, supported Vault release. Staying current mitigates security exposures and avoids unsupported features that might put your secrets at risk.
For robust Vault upgrades, Chkk supports both:
Each template details the exact steps, including data backups, unseal procedures, health checks, and rollback instructions.
Major or sensitive updates often warrant a “practice run.” Chkk’s preverification simulates your Vault configuration—auth backends, secrets engines, policies—in a safe environment. By applying the new version in a sandbox, Chkk identifies incompatibilities such as deprecated configuration parameters or plugin mismatches before they hit production. Early detection helps fix potential issues well before you’re managing them under pressure in a live environment.
Whether Vault is installed via Helm, Kustomize, or raw YAML, Chkk can parse your manifests and values to orchestrate safe and reliable upgrades. Chkk respects private registries, custom images, and your organization’s security constraints, ensuring you don’t have to refactor your preferred deployment approach just to keep Vault up to date.
Chkk Operational Safety Platform simplifies upgrades, reduces risk, and keeps your Kubernetes infrastructure operational. Here’s how that applies to HashiCorp Vault upgrades:
Try Chkk Upgrade Copilot to experience how these extended capabilities can simplify your upgrade processes for HashiCorp Vault and 100s of other Kubernetes add-ons. We look forward to helping you achieve seamless, secure, and efficient operations.
Click the button below to book a demo and learn more.