spec.clusterIP to skip headless Services.kubectl version --short | grep Server) or roll back the Kubelet if you already upgraded out‑of‑order.NOTE: You must upgrade the Kubernetes control plane to v1.31 and confirm the API server reports v1.31 before upgrading any worker nodes or Kubelets.
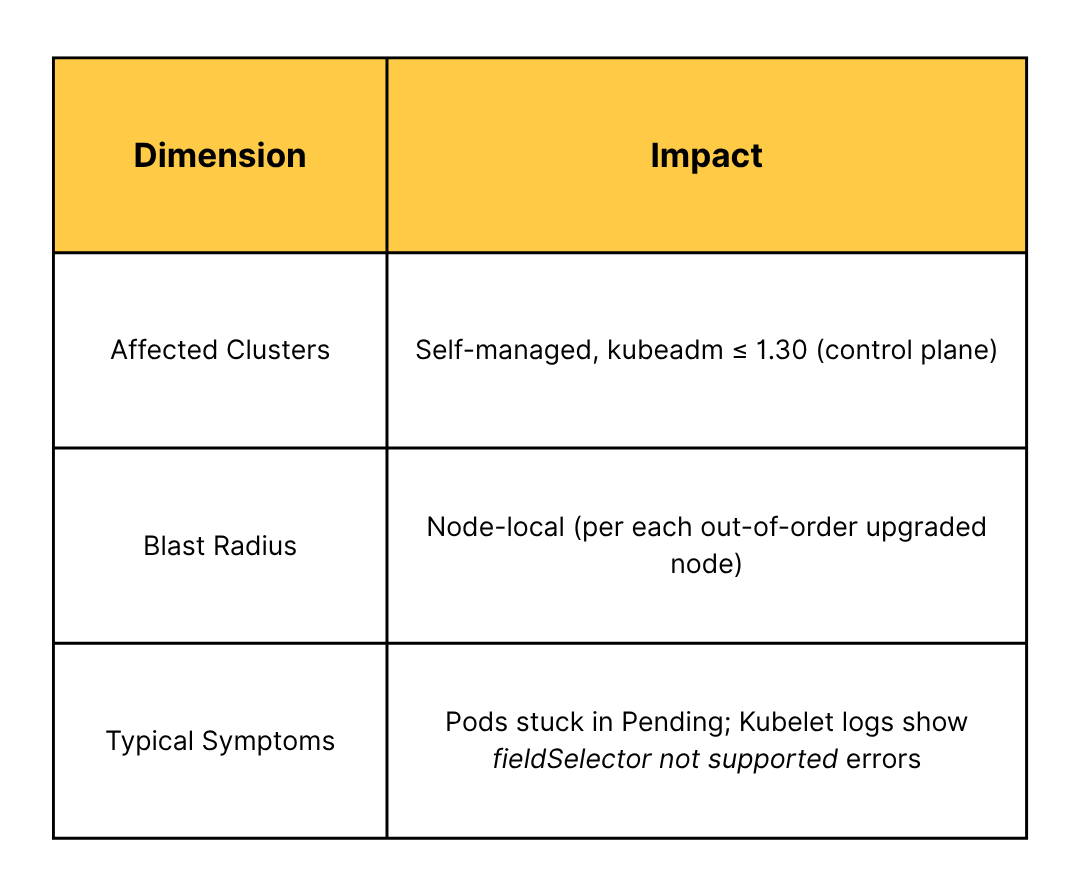
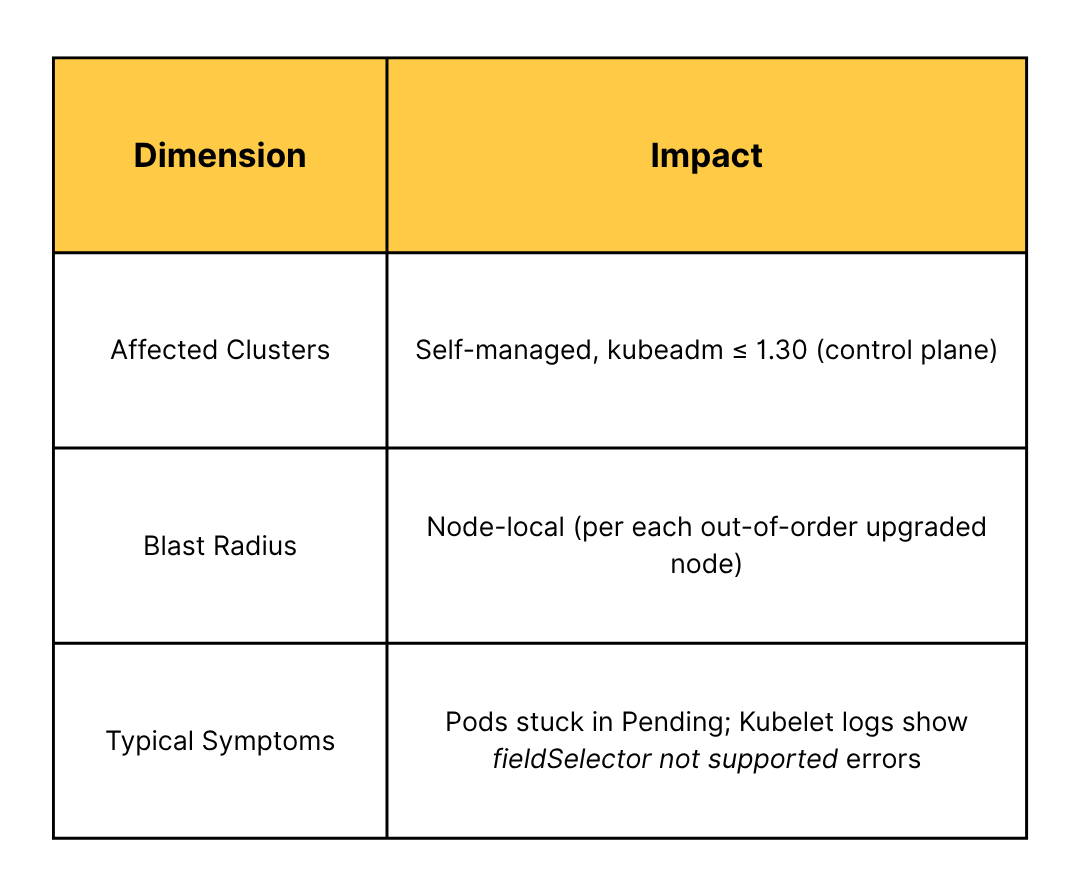
IMPACT: If a Kubelet is upgraded to v1.31 while its API server is still v1.30, pods on that node will fail to start because the older API server cannot parse the new spec.clusterIP selector. Upgrading in the wrong order expands the blast radius to the entire cluster and can cause downtime for all workloads.
Kubernetes 1.31 introduced a new field selector for Services on the clusterIP and type fields. The Kubelet uses this selector (spec.clusterIP!=None) to avoid watching headless Services and reduce memory usage.
This change means a Kubelet v1.31 will query the API server with that filter. If the API server is still on 1.30 or older (which doesn’t support filtering by spec.clusterIP), it will reject the request. In effect, the Kubelet can’t retrieve Service data, which disrupts its ability to start pods on that node (since it cannot set up environment variables and networking info from Services).
kubectl get pods -A --field-selector status.phase=Pending to identify any pods stuck in Pending (especially on newly upgraded nodes).kubectl version --short | grep Server to confirm the API server is exactly v1.31.x before upgrading any nodes.fieldSelector "spec.clusterIP!=None" not supported.E0518 10:32:44 … fieldSelector "spec.clusterIP!=None" not supported
The above error appears in the Kubelet logs when it fails to list Services. A Kubelet v1.31 issues a list/watch for Services with spec.clusterIP!=None. An older API server (v1.30) doesn’t recognize spec.clusterIP as a valid field selector and returns a 400 Bad Request error. This mismatch causes the Kubelet’s service watcher to crash out, preventing pods on that node from starting because required Service environment variables and cluster IP assignments can’t be initialized.
ControlPlaneKubeletLocalMode feature gate so each control‑plane Kubelet talks only to its own (already‑updated) API server.Chkk’s Upgrade Copilot not only analyzes release notes and changelogs but also identifies critical Upgrade Advisories based on real-world experiences from users and insights from our pre-verification process. This helps you proactively address potential risks or breakages during your Kubernetes upgrades or open-source project updates.
In addition to Upgrade Advisories, Chkk covers comprehensive tasks including Helm diffs, CRD diffs, dependency mapping, configuration validations, and deprecated API detection, providing thorough coverage of upgrade-related risks.
Click the button below to book a demo and learn more.
spec.clusterIP to skip headless Services.kubectl version --short | grep Server) or roll back the Kubelet if you already upgraded out‑of‑order.NOTE: You must upgrade the Kubernetes control plane to v1.31 and confirm the API server reports v1.31 before upgrading any worker nodes or Kubelets.
IMPACT: If a Kubelet is upgraded to v1.31 while its API server is still v1.30, pods on that node will fail to start because the older API server cannot parse the new spec.clusterIP selector. Upgrading in the wrong order expands the blast radius to the entire cluster and can cause downtime for all workloads.
Kubernetes 1.31 introduced a new field selector for Services on the clusterIP and type fields. The Kubelet uses this selector (spec.clusterIP!=None) to avoid watching headless Services and reduce memory usage.
This change means a Kubelet v1.31 will query the API server with that filter. If the API server is still on 1.30 or older (which doesn’t support filtering by spec.clusterIP), it will reject the request. In effect, the Kubelet can’t retrieve Service data, which disrupts its ability to start pods on that node (since it cannot set up environment variables and networking info from Services).
kubectl get pods -A --field-selector status.phase=Pending to identify any pods stuck in Pending (especially on newly upgraded nodes).kubectl version --short | grep Server to confirm the API server is exactly v1.31.x before upgrading any nodes.fieldSelector "spec.clusterIP!=None" not supported.E0518 10:32:44 … fieldSelector "spec.clusterIP!=None" not supported
The above error appears in the Kubelet logs when it fails to list Services. A Kubelet v1.31 issues a list/watch for Services with spec.clusterIP!=None. An older API server (v1.30) doesn’t recognize spec.clusterIP as a valid field selector and returns a 400 Bad Request error. This mismatch causes the Kubelet’s service watcher to crash out, preventing pods on that node from starting because required Service environment variables and cluster IP assignments can’t be initialized.
ControlPlaneKubeletLocalMode feature gate so each control‑plane Kubelet talks only to its own (already‑updated) API server.Chkk’s Upgrade Copilot not only analyzes release notes and changelogs but also identifies critical Upgrade Advisories based on real-world experiences from users and insights from our pre-verification process. This helps you proactively address potential risks or breakages during your Kubernetes upgrades or open-source project updates.
In addition to Upgrade Advisories, Chkk covers comprehensive tasks including Helm diffs, CRD diffs, dependency mapping, configuration validations, and deprecated API detection, providing thorough coverage of upgrade-related risks.
Click the button below to book a demo and learn more.